Scenario:
A customer has supplied you with a crash report containing a callstack with relative offsets from DLLs. The callstack also indicates which module relates to which address.
Example Data:
Exception code: C0000005 ACCESS_VIOLATION
Fault offset: 00x00036FA3 C:\WINDOWS\system32\MSVCRT.dll
Exception Parameters:
0: 0x00000000 [Read Error]
1: 0x5f8f2000 [Address]
Registers:
EAX:B3BEB6D4
EBX:5F8CB6C8
ECX:150BE5B5
EDX:00000000
ESI:5F8F2000
EDI:01B98DEC
CS:EIP:001B:77C46FA3
SS:ESP:0023:0012F158 EBP:0012F160
DS:0023 ES:0023 FS:003B GS:0000
Flags:00010212
StackTrace
C:\WINDOWS\system32\MFC42u.DLL : 0x0000270a
C:\Program Files\Software Verification\Memory Validator\memoryValidator.exe : 0x000db989
C:\Program Files\Software Verification\Memory Validator\memoryValidator.exe : 0x000db1f8
C:\Program Files\Software Verification\Memory Validator\memoryValidator.exe : 0x00121a83
C:\Program Files\Software Verification\Memory Validator\memoryValidator.exe : 0x00121b7e
C:\Program Files\Software Verification\Memory Validator\memoryValidator.exe : 0x00174ec5
C:\Program Files\Software Verification\Memory Validator\memoryValidator.exe : 0x00175094
C:\WINDOWS\system32\MFC42u.DLL : 0x00013724
C:\WINDOWS\system32\MFC42u.DLL : 0x00014245
C:\WINDOWS\system32\MFC42u.DLL : 0x00001b31
C:\WINDOWS\system32\MFC42u.DLL : 0x0008cba7
This is data from a real crash many years ago.
Question:
There are no DLL load addresses and the addresses aren't addresses, but offsets from the start of a DLL. How do you decode these relative offsets?
Answer:
In the above data we can see a callstack containing entries for mfc42u.dll, and memoryValidator.exe.
All the modules are Microsoft DLLs except for the EXE, which is part of C++ Memory Validator, one of our tools.
To decode these values, we load memoryValidator.exe into DWARF Browser.exe, then for each symbol we take the following actions.
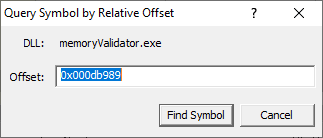
For our purposes here, we're going to show how to convert one symbol. We're going to use the first symbol from memoryValidator.exe in the example data above.
C:\Program Files\Software Verification\Memory Validator\memoryValidator.exe : 0x000db989
The relative address (or offset) is 0x000db989. We don't know the DLL load address.
From the Query menu choose Find Symbol with DLL Relative Address....
The Query Symbol by Absolute Address dialog is displayed.
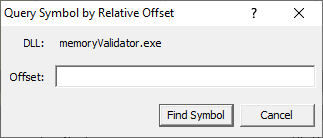
Type the relative address into the Offset field. Prefix any hexadecimal addresses with 0x.
Click the Find Symbol button.
The appropriate location in the code is found and displayed. In this example DWARF Browser could not locate the source code (as the file location is not valid on this machine)
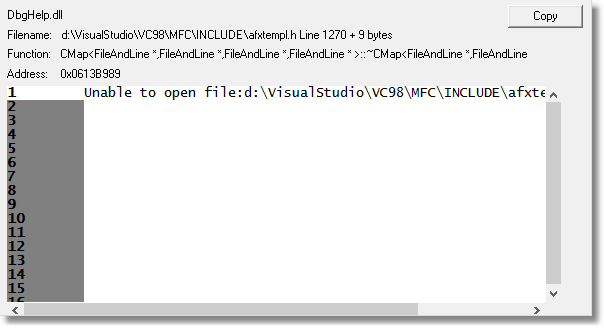
Results:
Repeating the process for the data shown above resulted in this information.
Exception code: C0000005 ACCESS_VIOLATION
Fault offset: 00x00036FA3 C:\WINDOWS\system32\MSVCRT.dll
Exception Parameters:
0: 0x00000000 [Read Error]
1: 0x5f8f2000 [Address]
Registers:
EAX:B3BEB6D4
EBX:5F8CB6C8
ECX:150BE5B5
EDX:00000000
ESI:5F8F2000
EDI:01B98DEC
CS:EIP:001B:77C46FA3
SS:ESP:0023:0012F158 EBP:0012F160
DS:0023 ES:0023 FS:003B GS:0000
Flags:00010212
StackTrace
C:\WINDOWS\system32\MFC42u.DLL : 0x0000270a
C:\Program Files\Software Verification\Memory Validator\memoryValidator.exe : 0x000db989 CMap<...big template definition...> afxtempl.h 1270
C:\Program Files\Software Verification\Memory Validator\memoryValidator.exe : 0x000db1f8 CMap<...big template definition...>::~CMap<...big template definition...> afxtempl.h 1270
C:\Program Files\Software Verification\Memory Validator\memoryValidator.exe : 0x00121a83 CVirtualTreeBase::Draw VirtualTreeBase.cpp 176
C:\Program Files\Software Verification\Memory Validator\memoryValidator.exe : 0x00121b7e CVirtualTreeBase::Draw VirtualTreeBase.cpp 198
C:\Program Files\Software Verification\Memory Validator\memoryValidator.exe : 0x00174ec5 LocalAllocStackTrace::getStringRepresentation LocalAllocTrace.cpp Line 182
C:\Program Files\Software Verification\Memory Validator\memoryValidator.exe : 0x00175094 LocalFreeStackTrace::getStringInfo LocalAllocTrace.cpp 296
C:\WINDOWS\system32\MFC42u.DLL : 0x00013724
C:\WINDOWS\system32\MFC42u.DLL : 0x00014245
C:\WINDOWS\system32\MFC42u.DLL : 0x00001b31
C:\WINDOWS\system32\MFC42u.DLL : 0x0008cba7